Abstract
Satellite internet based on 5G/6G integrates security and communications and represents a future direction for network design. After analyzing networking and security issues for 5G/6G satellite internet, this article proposes an overall approach for integrated security and communication design, outlines a unified architecture for satellite internet and security integration, and further proposes a closed-loop management mechanism and a self-learning growth mechanism. The proposals provide design reference for satellite internet construction in China.
Introduction
In recent years, the demand to integrate 5G/6G and satellite networks has grown. As leading infrastructure, 5G/6G has driven digital transformation. In sparsely populated remote areas or during disaster response, terrestrial networks are less economical and less resilient than satellite networks and are harder to maintain. Therefore, integrating 5G/6G with satellite networks is an effective solution to achieve ubiquitous connectivity.
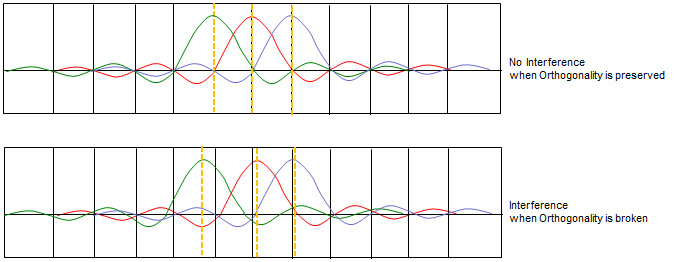
3GPP divides the integration of 5G/6G and satellite internet into two stages: the first stage is satellite systems accessing the 5G/6G core network, where satellites act as access and transport networks; the second stage is integrating satellite systems with 5G/6G over the air interface, making satellite air interface protocols compatible with 5G/6G air interface protocols. With minor frequency allocations, satellite base stations can act as 5G/6G base stations and satellite terminals can become ordinary 5G/6G terminals.
Thus, satellites can complement terrestrial 5G/6G as an access or backhaul method, enabling flexible space-and-ground integrated networks and achieving comprehensive coverage.
1. 5G/6G Satellite Internet Networking and Security Analysis
1.1 ITU Four Networking Scenarios
ITU-R M.2460, "Key Elements for Integration of Satellite Systems into Next Generation Access Technologies," defines and analyzes satellite network application scenarios, service scopes, and key technologies. The report identifies four space-ground integration application scenarios, shown in Figure 1.

Figure 1 ITU four satellite internet application scenarios
(1) Relay to station. Use satellite links to extend connectivity to local cell sites (for example 3G/4G/5G cellular networks), extending local routing to interconnect remote services and reducing latency.
(2) Cell backhaul. Use satellite point-to-multipoint multicast functions to deliver remote services to local networks and transmit local network data to remote sites.
(3) Communications for moving platforms. Satellite links provide connections to fast-moving platforms such as aircraft, vehicles, trains, and ships, leveraging satellites' wide coverage for efficient links.
(4) Hybrid multicast scenarios. In mixed multimedia communication scenarios, satellites can service homes and offices to supplement terrestrial broadband, relieve terrestrial network congestion, and support large-scale broadband demands (video, HDTV, and other non-video data).
Based on these service descriptions and topologies, satellites play a key role as wireless backhaul networks in the ITU four scenarios, transporting local data to remote sites or vice versa. With access-backhaul unified designs in 5G/6G wireless technologies, satellite networks based on 5G/6G can readily realize these transport functions. A 5G satellite integrated transport view is shown in Figure 2.

Figure 2 5G satellite integrated transport view
In this scenario, some signals access satellite base stations via backhaul terminals (which can be 5G terminals or modules) to transmit terrestrial data via satellite to remote locations; other terrestrial terminals connect directly to satellites. Satellites then deliver data to the terrestrial core network over feeder links using 5G air interface methods, integrating with terrestrial 5G infrastructure.
The same access-backhaul unified design principles apply to 6G.
1.2 Security Issues in 5G/6G Satellite Networking
Space-and-ground integrated networks that fuse 5G/6G with satellite internet can inherit current 5G security measures, but introducing space-based networks and satellite mobility introduces new security risks.
Figure 3 shows an evolved space-ground integrated architecture derived from 5G/6G developments, where satellite and terrestrial access complement each other and ground and on-board control coexist. Access terminals can maintain dual connectivity to satellite and terrestrial base stations. Core networks may include both space-based and ground-based cores, and may gradually converge into a unified network as services evolve.
(1) More granular terminal security. In a space-ground integrated network, terminals may connect to both satellite and terrestrial base stations concurrently. The two service paths may carry different service attributes and security levels. Access control must handle disparate security levels; asynchronous links require the terminal to allocate separate resources for processing and storage; terminals must support fine-grained security management of software and hardware. Additionally, terminals must separately maintain signaling and data integrity and confidentiality protections and handle mobility security for both space-based and ground-based services, greatly increasing terminal complexity.
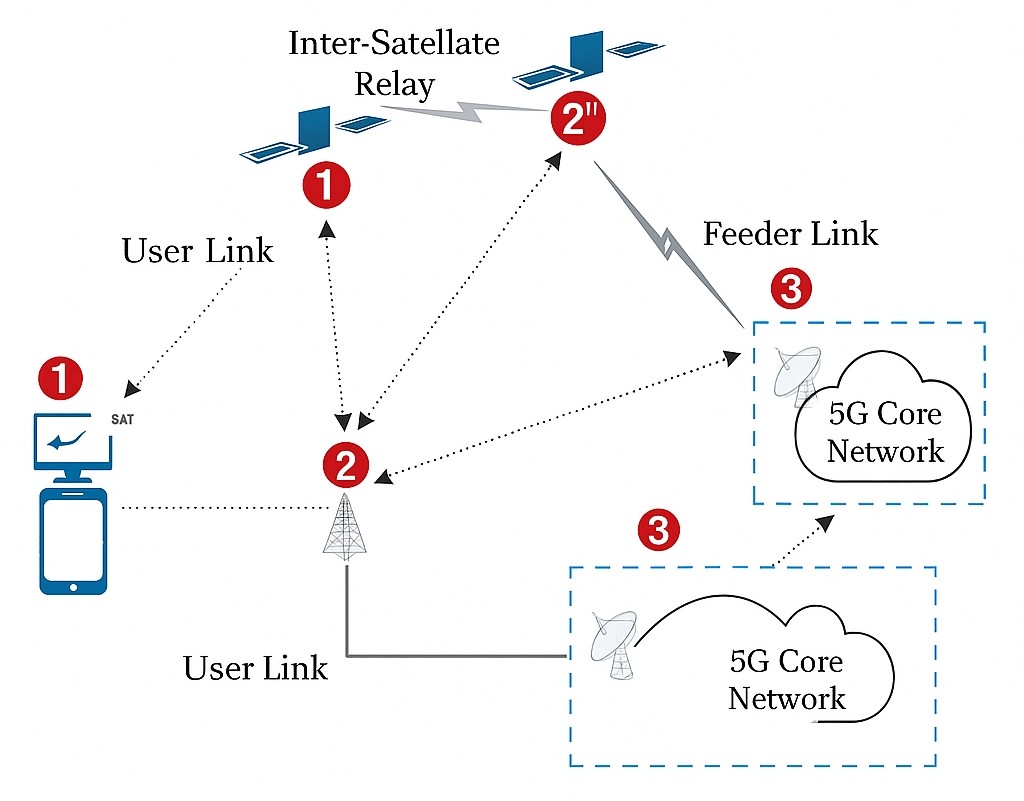
Figure 3 Space-ground integrated network architecture
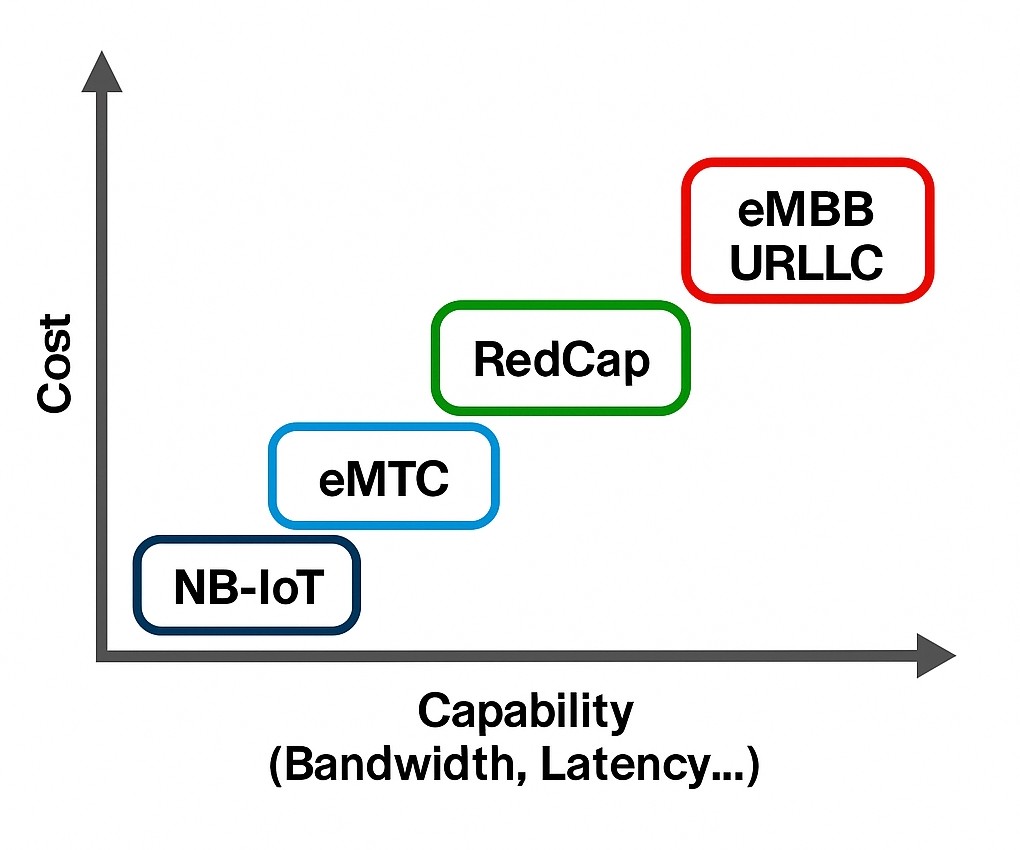
(2) More autonomous access security. The integrated coverage is broader and access networks are highly heterogeneous, increasing security autonomy. Different device groups and user groups require independent clusters with their own security attributes and exclusivity. By combining cells, sectors, and heterogeneous cascaded networks with security controls, air interface access can be managed. A heterogeneous access space-ground integrated network architecture is shown in Figure 4, where independent access resources, group IDs, group keys, and group data protection methods are allocated to cells. Satellite mobility leads to frequent resource handovers, increasing the complexity of security processing.

Figure 4 Heterogeneous access space-ground integrated network architecture
(3) Highly coordinated network security. Space-ground integrated networks exhibit new, complex application scenarios, time-varying topology, and mixed diverse services, requiring high coordination across network segments to achieve complex routing and end-to-end service and security guarantees. Space-based internet scheduling is highly dynamic, and multiple link segments must coordinate closely to provide end-to-end functionality and security. An example of space-ground integrated application services is shown in Figure 5.

Figure 5 Space-ground integrated application services
2. Research on Integrated Satellite Network Security
With the development of satellite communications, space networks and ground networks will evolve toward integrated operation, converging application services, network architectures, and core networks. Space-ground coordinated resource scheduling will enable on-demand resource allocation and optimal data flows, building global space-ground integrated networks capable of self-configuration, self-repair, and self-optimization.
Under this network convergence, generational network effects increase and security measures must be reinvented. Traditional approaches that add security products after network deployment, or maintain separate communication and security stacks, will be inadequate in highly dynamic architectures and will be phased out.
Security must be integrated with the network and designed holistically. Security should become an intrinsic network factor, embedded into compute and storage resources and treated as a network resource component that co-evolves with the network. Security should be service-oriented and orchestrated according to network needs.
2.1 Overall Security Assurance Approach for Satellite Internet
Anticipating future 5G/6G satellite internet developments and applications, we propose a foundational design for satellite internet security assurance. Starting from 5G and facing 6G, satellite internet will evolve into a new space-ground integrated network exhibiting self-configuration, self-repair, and self-optimization.
2.1.1 Reconstruct security resources
Space-ground integrated networks will share infrastructure to provide differentiated services to public, industry, and special users. This requires combining diverse resources to meet heterogeneous needs, with unified orchestration and tiered protection to prevent side-channel attacks and threat propagation. Traditional monolithic security resources should be granularized into dynamic, heterogeneous, and redundant security resources so the network can select and recompose them per demand. Security resources should be tiered and fully service-enabled so that resources at the same security level are reusable: when a service starts, some security resources are occupied; when the service ends, those resources are released and can be recomposed for other tasks.
2.1.2 Internalized security factors in the network
To allocate security and network resource blocks on demand, security factors must be embedded as services throughout the network. First, integrate security hardware entities with network hardware entities so they co-design at the processor level for future networks. Second, split security hardware into fine-grained components and package each as a service to reduce coupling and increase reuse. Finally, use software-defined security functions to provide virtualized security services to applications and enable interoperability with other network security functions.
2.1.3 Unified identity and trust framework
5G/6G satellite internet aims to enable full mobility and ubiquitous connectivity for applications such as VR/AR, smart cities, smart agriculture, maritime operations, desert operations, industrial internet, vehicular networks, autonomous driving, smart homes, telemedicine, drones, and emergency response. The ecosystem includes traditional service providers, operators, equipment vendors, users, and new roles such as edge computing providers, IoT service platforms, dedicated business systems, cloud operators, and device owners. The satellite internet ecosystem is therefore more complex and requires a security framework that defines roles, security boundaries, and responsibilities to establish an end-to-end trust model that unifies the segmented satellite internet into a coherent whole.
2.2 Overall Security Architecture
Based on the above, this article proposes a cryptography-based space-ground integrated network security architecture for 5G/6G, as shown in Figure 6. The first layer is the security support layer, including cryptographic resource pools, identity management, security policies, security services, secure storage resources, and secure compute resources. Security genes are embedded into network resources to support network construction. An end-to-end unified identity and trust framework provides infrastructure trust and identity and data trust. The second layer is the security service layer, which uses the first-layer resources to build terminal security services, access security services, network security services, and mobility security services, offering graded protection for network nodes. The third layer is the network-wide security layer, forming a closed-loop security system where terminals, network elements, and boundaries in a highly dynamic satellite internet achieve integrated security, ultimately building a self-aware and self-growing secure network based on embedded security factors.
In this architecture, digital and reconfigurable cryptographic techniques are treated as network genes implanted at the network base layer and co-orchestrated and grown with the network to form innate immunity. As the network evolves, cryptographic techniques also learn and develop, enabling security to grow adaptively.

Figure 6 5G/6G space-ground integrated network security architecture
2.2.1 Closed-loop management
Within the 5G/6G space-ground integrated network security architecture, security and network resources are unified in architecture, services, and orchestration. Figure 7 abstracts a closed-loop management process for security network resources. Using cryptographic situational awareness, security resources can dynamically adjust based on network demand and changes to support a future self-intelligent satellite internet security network.

Figure 7 Closed-loop management of space-ground integrated network security resources
2.2.2 Cryptography as foundation and adaptive growth
Since 2G, cryptographic techniques have co-evolved with communication technologies and have continued through 3G/4G/5G. In 5G, cryptography supports infrastructure security via primary authentication, secondary authentication, communications techniques, OAuth 2.0, and confidentiality and integrity protections. Historically, confidentiality protections and transmission encryption are seldom fully enabled in live networks because security impacts network efficiency and reduces spectrum utilization.
However, as network capacity and utilization increase, security incidents will multiply as attackers target valuable enterprise and personal data.
Therefore, the design of a 5G/6G integrated satellite internet must balance security costs and network performance from the outset. Cryptographic digital signal processing logic units should be co-designed with underlying compute and storage logic units to maximize hardware efficiency. Only by doing so can constrained and highly dynamic satellite internet resources be accommodated, treating cryptography as a network quality factor that is co-orchestrated and co-reconstructed with network resources as the network autonomously learns and grows.
3. Conclusion
5G/6G satellite internet is a progressively integrated network across space, ground, sea, and air and represents convergence across digital operations, intelligence, communication, and trust. It also represents an integration of security and communications and a direction for future networks. The proposed cryptography-based satellite network security architecture embeds security factors into the infrastructure layer and coordinates orchestration and flexible scheduling to build a secure satellite internet.
Using the proposed architecture as a reference, security services can be provided across terminal, access, transport, and application layers to build an end-to-end space-ground integrated security service system for satellite communications.
 ALLPCB
ALLPCB