Overview
As people benefit from smart technology, vulnerabilities hidden in edge devices can lead to serious security incidents. ATMs, payment terminals, vending machines, ticket kiosks, CT scanners and other large medical equipment, and even automated fueling stations can be exploited by attackers to steal financial and other sensitive data.
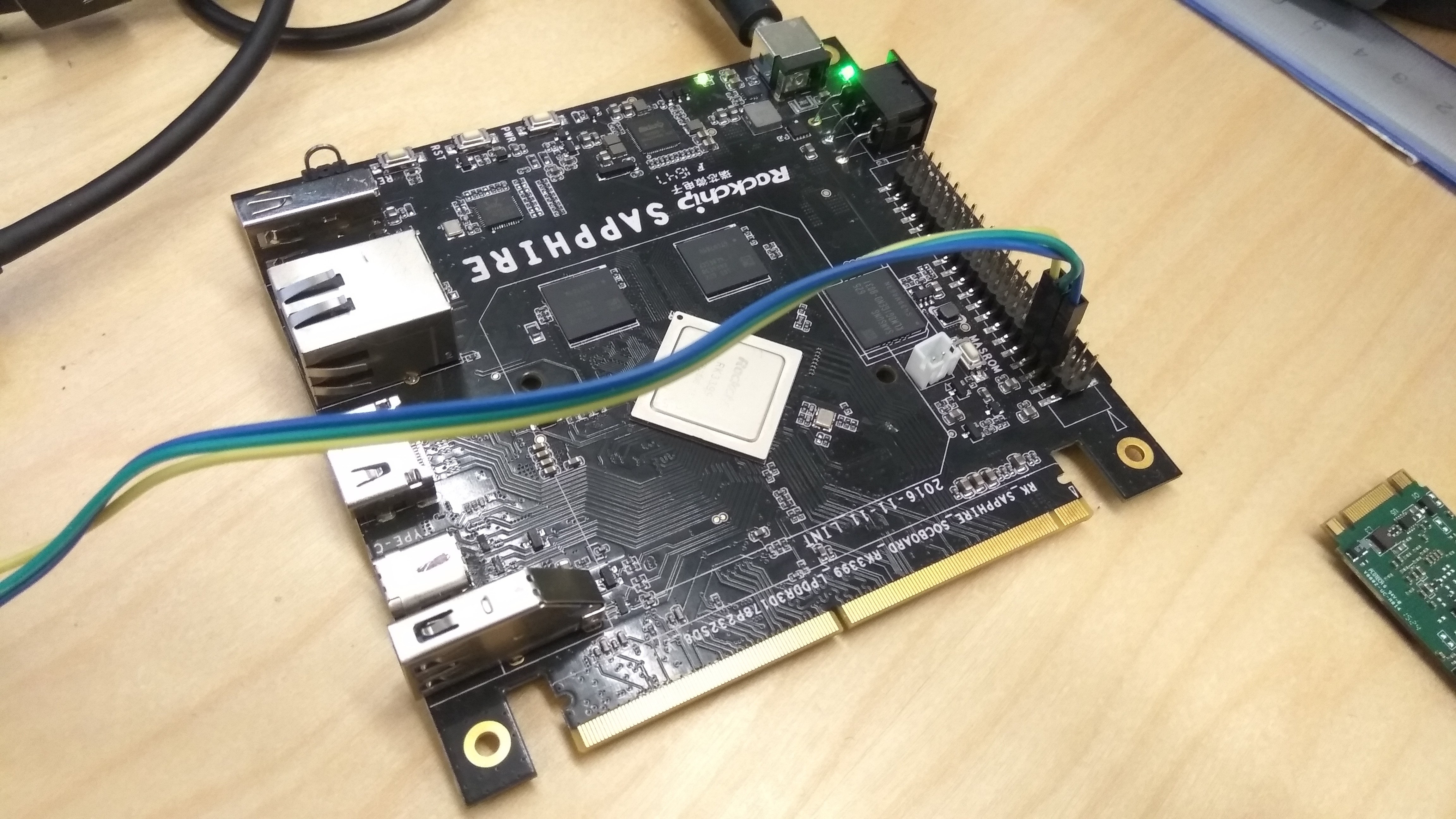
In practice, Internet of Things (IoT) systems often place many devices outside traditional security perimeters, and those devices are easily targeted by network attacks. Limited computing resources on edge devices constrain available defenses, making them susceptible to overload attacks. Designs that rely on third-party libraries and frameworks, particularly open source components, carry elevated risk. Securing these edge devices has become an important consideration in embedded system design.
Expanded Attack Surface and Heterogeneity
IoT represents a large-scale expansion of the network environment by connecting countless devices, from household appliances to industrial sensors. This connectivity brings efficiency but also greatly expands the attack surface. The heterogeneity and sheer number of IoT devices make it extremely difficult to maintain a consistent security posture, creating demand for robust and adaptive embedded security solutions.
Many embedded systems are becoming increasingly complex as they replace human decision-making or offer capabilities beyond human limits. For example, systems used in aircraft and in drones can fuse sensor data and act faster than a human operator.
Primary Security Challenges
- Diverse architectures
- Limited resources
- Insecure network connectivity
- Long lifecycles and associated risks
- Third-party components
Edge embedded systems require strong security measures, yet most embedded engineers are not security specialists. This gap has led to the adoption of decentralized security frameworks based on the zero trust principle and emphasizing the CIA triad (confidentiality, integrity, and availability). In the context of embedded security, the CIA triad helps guide the development and implementation of measures tailored to the unique challenges these systems face.
Design and Implementation Approaches
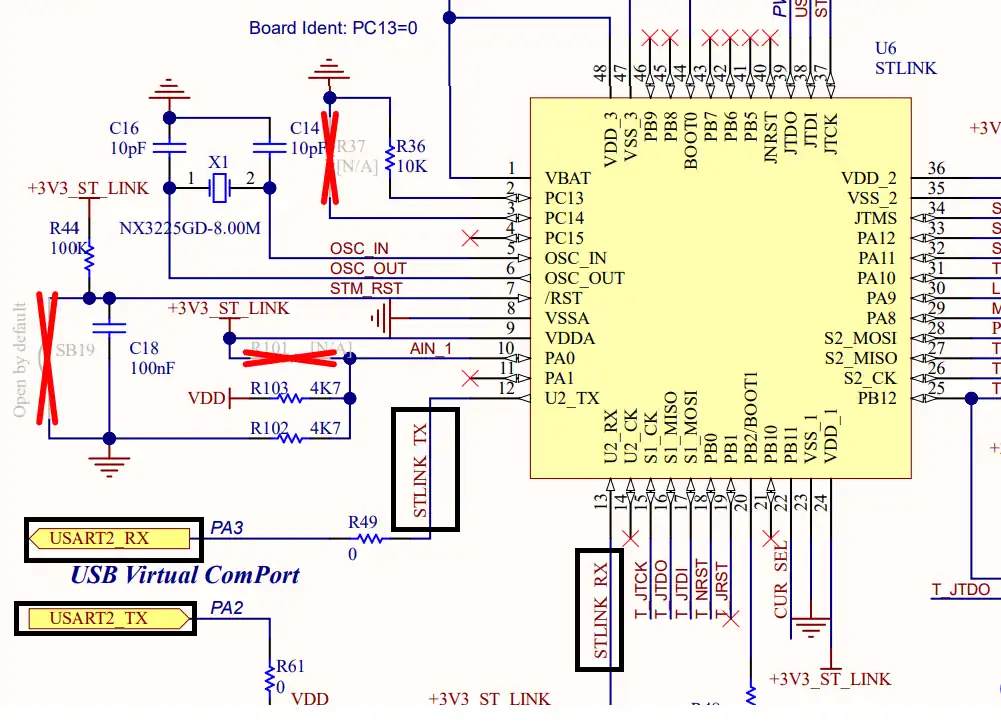
Integrating the CIA triad into embedded security strategies requires a comprehensive approach that addresses both digital and physical concerns. Typical measures include hardware-based security features, secure boot processes, access control, and rigorous testing and verification to identify and mitigate vulnerabilities.
Implementing these measures during system design demands careful balancing of security, resource constraints, and operational requirements. Common practices include:
- Secure-by-design considerations
- Risk assessment
- Selecting robust security architectures
Limited processing power and small memory footprints in many embedded systems pose significant obstacles to implementing full-featured security. Recent trends show a shift toward strengthening security at the hardware level so devices are more secure from initial deployment.
Role of AI and Machine Learning
Artificial intelligence and machine learning are increasingly being incorporated into embedded systems to enhance functionality and security. These algorithms have advanced threat detection, data leakage prevention, and vulnerability mitigation. Combined with hardware protections, AI and machine learning can enable more sophisticated security for future embedded systems.
 ALLPCB
ALLPCB