Overview
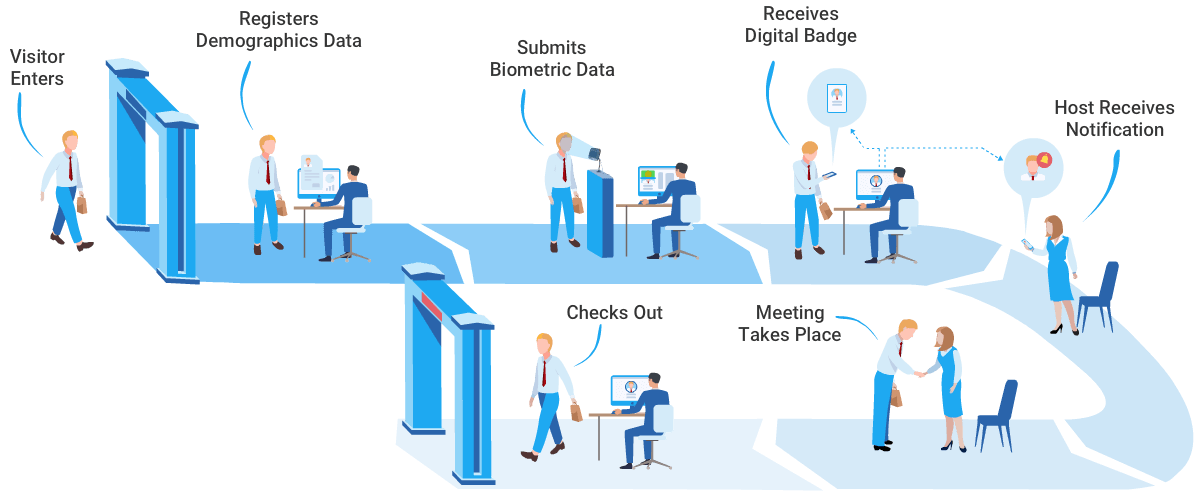
Iris recognition is an identity verification method based on the iris. It is used in security devices, such as access control, and in locations that require high confidentiality. Iris recognition is a type of biometric identification.
Eye anatomy and iris uniqueness
The eye consists of the sclera, iris, pupil, lens, retina, and other parts. The iris is the annular region located between the dark pupil and the white sclera. It contains many interlaced spots, filaments, coronas, furrows, and other fine features. The iris forms during fetal development and remains stable throughout life. These characteristics make the iris unique and suitable for personal identification.
Recognition process
Iris recognition determines identity by comparing similarities between iris image features. The process typically includes four steps:
-
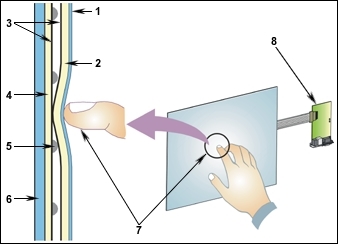
Iris image capture
Capture the entire eye using specialized imaging equipment and transmit the images to the iris recognition system's image preprocessing software.
-
Image preprocessing
Process the acquired iris image to prepare it for feature extraction.
Iris localization: determine the positions of the inner and outer circles and the eyelid curves in the image. The inner circle is the boundary between the iris and the pupil; the outer circle is the boundary between the iris and the sclera; the eyelid curves correspond to the upper and lower eyelid boundaries.
Iris normalization: resize the iris region to a fixed size required by the recognition system.
Image enhancement: adjust brightness, contrast, and smoothing on the normalized image to improve the detectability of iris features.
-
Feature extraction
Use specific algorithms to extract characteristic features from the iris image and encode them.
-
Feature matching
Compare the encoded features to entries in a database to determine whether they correspond to the same iris, thereby confirming identity.
Advantages
- User-friendly.
- Potentially one of the most reliable biometric techniques.
- No physical contact required.
- High reliability.
- Fast and convenient: no documents are required for access control; systems can operate unidirectionally or bidirectionally and can authorize one or multiple doors.
- Flexible authorization: user privileges can be adjusted as needed, and the system can log user identity, operation location, functions, and timestamps to support real-time management.
- Difficult to forge: iris data serves as the credential and is hard to replicate. Activities can be automatically logged for auditing, and the system can trigger alerts for suspicious events.
- Flexible configuration: installation and operation modes can be adjusted to suit users or administrators. For example, in public areas a password-only mode may be used, while in more secure settings passwords can be disabled and only iris recognition allowed; hybrid modes are also possible.
- Low modification and maintenance needs: installation can retain existing locks while reducing mechanical moving parts and wear on bolts. The system requires minimal maintenance and can be expanded or upgraded without replacing hardware. Over time, this can improve operational efficiency and management level.
- Wide range of applications: used in industries such as mining, banking, corrections, access control, social security, and healthcare.
Limitations
- Difficult to miniaturize image acquisition equipment.
- High equipment cost, limiting widespread deployment.
- Lens distortion can reduce reliability.
- Two main modules: hardware and software.
- An automated iris recognition system comprises two main modules: the iris image acquisition device and the iris recognition algorithm, corresponding to the core issues of image capture and pattern matching.
 ALLPCB
ALLPCB