Introduction
What is face recognition, how does the technology work, and what steps are involved in implementing it? This article provides a primer on the principles and process of face recognition.
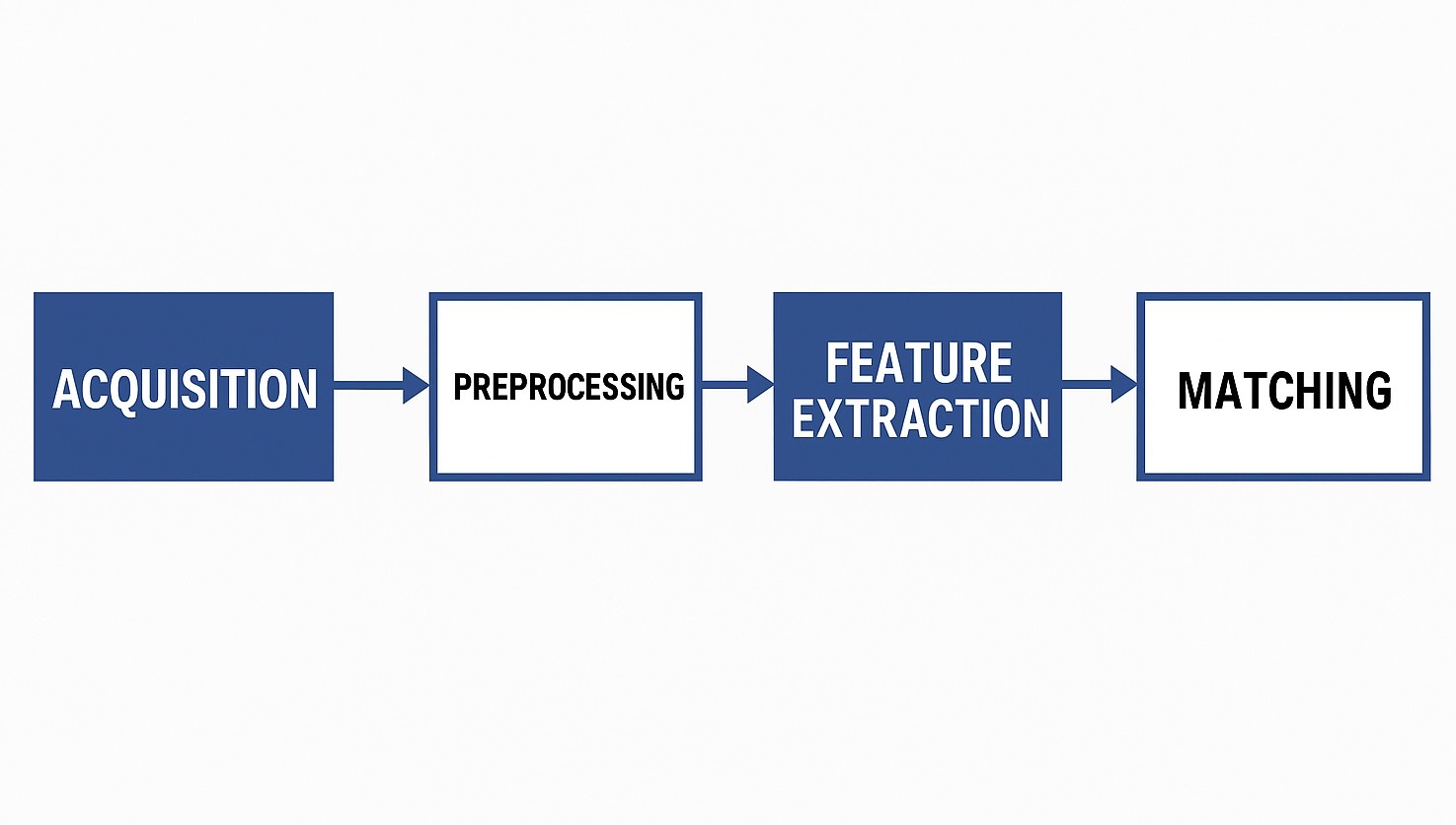
Face recognition is essentially a biometric identification technology. Broadly speaking, it refers to a complete system built on several technical bases, including face image acquisition and detection, data preprocessing, feature extraction, and matching. In recent years the technology has matured, and more providers offer end-to-end face recognition services.
High-level Steps
At a high level, face recognition involves three main steps: build a database containing many face images, acquire the target face image to be identified, and compare the target image against the database. The detailed implementation can be divided into four parts: face image acquisition and detection, data preprocessing, feature extraction, and matching and identification.
1. Face Image Acquisition and Detection
This part can be separated into image acquisition and face detection.
Image acquisition
Face images are commonly obtained by two methods: batch import of existing face images or real-time capture.
- Batch import of existing face images: face images obtained by various means are imported into the recognition system in bulk. The system then extracts facial data from each image automatically.
- Real-time capture: a camera or high-definition camera captures face images within its field of view and extracts faces in real time.
Face detection
A high-resolution photo that contains a face may also include other content, so face detection is required. The system locates the face region and estimates its size, selecting useful image data while removing irrelevant content to ensure accurate face extraction.
2. Data Preprocessing
The goal of data preprocessing is to prepare detected face images for reliable feature extraction. Preprocessing typically includes adjustments for illumination, rotation correction, cropping, filtering, denoising, and resizing. These steps ensure that the face image meets the requirements for subsequent feature extraction regardless of lighting, pose, distance, or size.
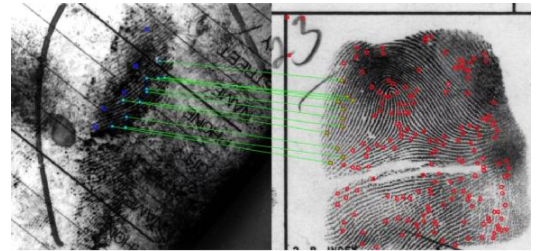
3. Feature Extraction
Modern face recognition systems extract features that represent visual characteristics of the face. Common approaches include appearance-based methods (e.g., pixel-based representations) and geometry-based methods that describe relative positions of facial landmarks.
For example, knowledge-based or geometric methods model the face by key components such as eyes, forehead, nose, ears, chin, and mouth, and describe the spatial relationships among these components. Each face can thus be represented by a set of geometric features that help distinguish one individual from another.
4. Matching and Identification
The system computes similarity scores between the extracted features of a target face and the feature templates in the database. A similarity threshold can be set so that faces exceeding the threshold are returned as candidates. Further filtering uses the similarity level and associated identity information.
Identification can be performed as:
- One-to-one (1:1) verification: confirm that the target face matches a claimed identity.
- One-to-many (1:N) search: compare the target face against many templates to find the best matches automatically.
Summary
In short, face recognition involves building a face image database, extracting target face images, and performing comparisons and filtering. The technical pipeline comprises face image acquisition and detection, data preprocessing, feature extraction, and automated matching and identification. Images can be sourced by batch import or real-time capture; preprocessing and detection ensure images meet feature extraction requirements; features are extracted using geometric or appearance-based methods; and matching is performed via thresholded similarity checks in 1:1 or 1:N modes.
 ALLPCB
ALLPCB