Introduction
With ongoing development, face recognition technology has gradually entered everyday use. Recently, a major webmail provider announced plans to use face recognition for login security, prompting questions about its practical applications and effectiveness. However, face recognition is not infallible and cannot currently achieve a 100% recognition rate.
Web Trials of Face Recognition
Face recognition systems are now used in a wide range of sectors, including public security, airports, border control, and safety monitoring, as well as civilian markets such as smart access control, locks, and attendance systems. The technology has begun to appear on internet services where users with cameras can opt in to capture facial data for comparison.
According to the provider, users could choose to require face authentication when logging in from a different location, or use face authentication to unlock accounts after repeated incorrect password attempts. The provider also claimed a recognition rate close to 100%, with resilience against photo spoofing and robustness to changes such as aging, makeup, or injury across different environments and lighting.
Application Categories
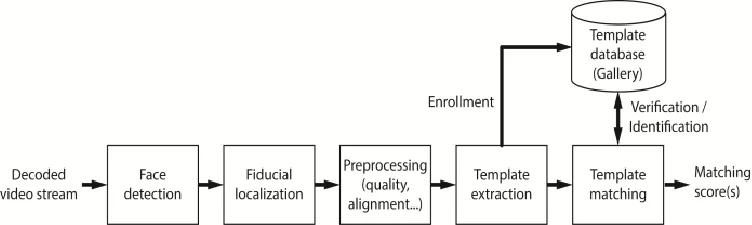
Face recognition involves more than taking a photo and comparing it. It includes a series of computations and transformations. From an application perspective, face recognition includes identification, which determines who a person is from a facial image, and verification, which confirms whether a face in an image matches a specified person.
Professor Tan Xiaoyang of Nanjing University of Aeronautics and Astronautics, who researches face recognition, explained these distinctions and their practical implications. Professor Su Guangda of Tsinghua University, involved in research under China's 863 Program, noted that after about 40 years of development, face recognition technology has reached a certain level of maturity and offers practical advantages compared with other biometric methods.
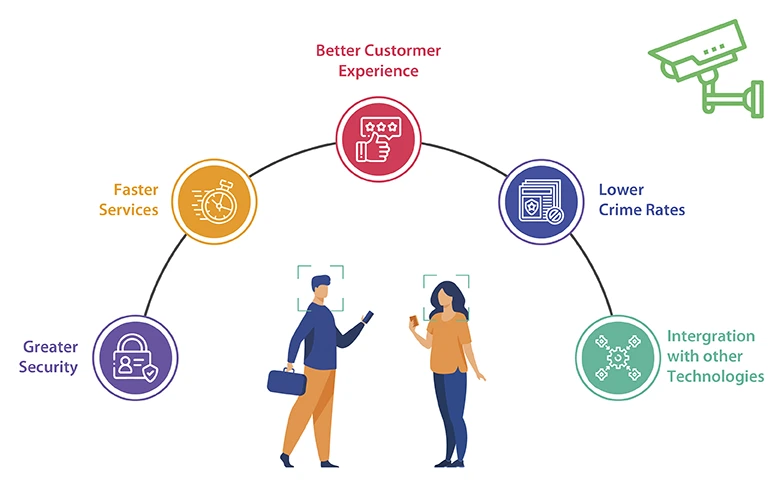
Su added that face recognition can be performed without user cooperation, which is useful for surveillance and law enforcement. It uses non-contact acquisition and is generally more acceptable than methods like fingerprint or palmprint capture. Its biggest advantage is that it aligns with human recognition habits, facilitating human-machine interaction and a range of applications from public safety to financial security and user interfaces.
Recognition Accuracy
Current face recognition systems can produce satisfactory results under ideal cooperation and acquisition conditions. However, when users are uncooperative or acquisition conditions are poor, recognition rates can drop sharply. The technology still faces many challenging problems.
Changes in appearance such as shaving, haircut changes, wearing glasses, or altered expressions can cause comparison failures. Even small changes may lead to authentication failure. A conservative estimate places current accuracy around 95%, not 100%. Identical twins present a particular challenge because of their very similar features, making reliable differentiation difficult.
Zhang Xiaobo of the Institute of Automation, Chinese Academy of Sciences, noted that lighting, pose, and accessories affect machine recognition. Even the most advanced systems tested abroad report false recognition rates around 1% under test conditions.
Unresolved Challenges
Occlusion is a serious issue for non-cooperative image capture, especially in surveillance, where subjects may wear glasses, hats, or other items that make facial images incomplete and degrade feature extraction and recognition. This can even cause face detection algorithms to fail. Effectively removing the impact of occlusions remains an urgent research topic.
Aging also affects facial appearance, particularly for adolescents, and recognition algorithms perform differently across age groups. Addressing the impact of age variation is necessary. As face databases grow in scale, algorithm performance may decline; maintaining or improving recognition rates in large-scale deployments is another important problem.
Any new technology brings both promise and practical limits. Bridging the gap between ideal expectations and real-world performance requires rigorous, step-by-step development.
The Face Recognition Process
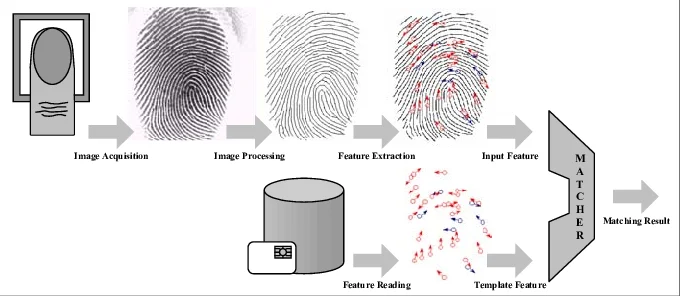
The typical process begins with face detection, which determines whether input images contain faces and, if so, returns the position and size of each face. Next is facial feature localization, which detects the positions and shapes of key facial components. Finally, the system performs face comparison by matching the localized features against a database to determine identity.
Security Considerations
Face recognition systems generally store information in machine-readable formats such as numbers or specific codes, and therefore face data can be targeted by hackers. Encrypting stored facial data can prevent stolen face data from being used or interpreted by unauthorized parties.
 ALLPCB
ALLPCB