Overview
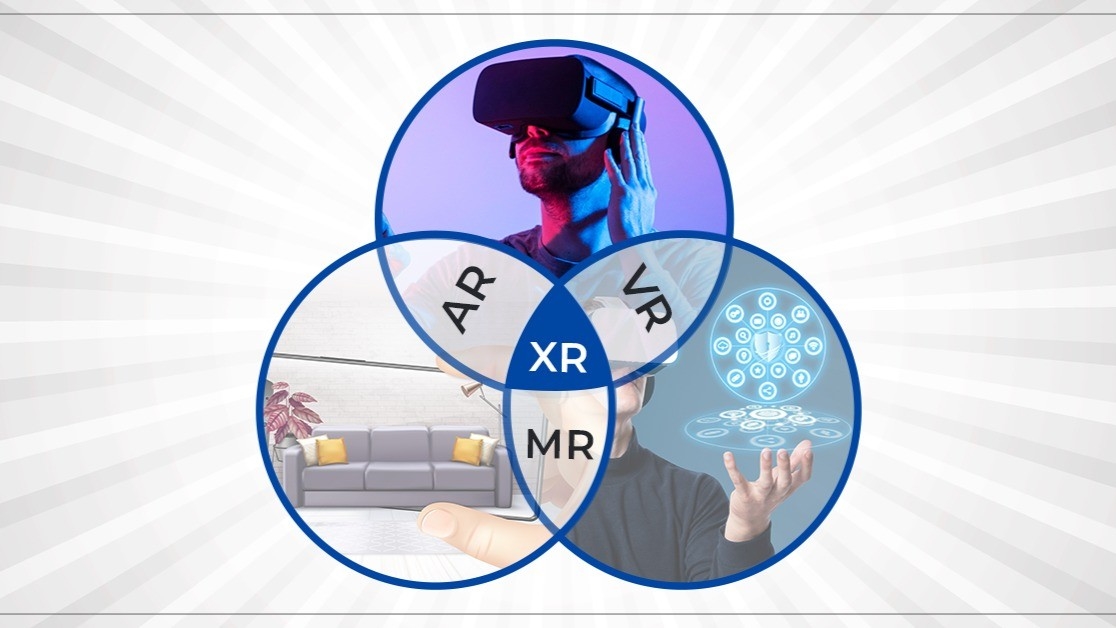
Regardless of how widespread immersive technologies become, organizations should remain aware of potential vulnerabilities and cybersecurity challenges associated with virtual reality (VR) and augmented reality (AR).
Entertainment innovations have repeatedly changed how people consume media. From newspapers to radio, from television to smartphones, discovery and access methods have evolved. Since the emergence of virtual reality and augmented reality, media usage and user preferences have continued to shift. Whether extending synthetic content into the real world or fully immersing users inside a virtual environment, AR and VR can change how people live, socialize, and play. However, alongside these new experiences there are cybersecurity challenges that may hinder some applications of these technologies, and those challenges warrant careful examination.
Security Challenges for VR and AR
Analysts expected the AR and VR market to grow rapidly. As these technologies mature and become mainstream, malicious actors are likely to experiment with ways to disrupt user experiences.
For example, imagine visiting a new location and using an AR-based navigation app on your smartphone to overlay street directions while you walk. What if hackers manipulated the navigation data? What if an infected navigation app provided incorrect routes or highlighted restaurants that match your preferences but lead you to empty storefronts? What if attackers leaked your current location to criminals? Such incidents may not be widespread now, but attackers have the capability to perform these actions. These risks must be considered and mitigated in advance.
New Data, New Risks
Earlier, when applications ran primarily on desktop computers, companies could only collect limited user data such as browsing patterns or site interactions. Since the arrival of smartphones, organizations have been able to collect richer user data including location, preferences, and interests. With IoT sensors, companies can obtain even more accurate and in-depth information about customers. The development of VR and AR further expands data collection capabilities.
Examples of data sources in AR/VR devices include:
- Headsets equipped with cameras and motion sensors that capture head and eye movements.
- Microphones included in headsets for interactive experiences such as virtual meetings, capturing spoken audio.
- Gesture-recognition systems that record meaningful information about a user's body movements.
- Precise location data used by location-dependent applications, such as location-based games like Pokémon Go.
Currently, this user information is managed and controlled by AR/VR companies. That is partly because there are few established regulations or strict guidelines governing these technologies, and partly because AR/VR is still maturing. Even if companies are transparent about data collection, storage, access, sharing, and processing, attackers can still steal data by malicious means.
Given the types of data AR/VR systems collect, the following challenges are likely to arise in the coming years.
Threat Examples
Surveillance
Data stored by AR/VR companies can be accessed not only by those companies but also by malicious actors. If attackers steal data and demand ransom, users and organizations may face difficult choices. There is also the policy question of whether users want their data collected, viewed, and used in real time.
DDoS Attacks
Imagine sitting in a cafe with friends while using VR. Suddenly a friend starts acting strangely, things freeze, and then your view goes blank. A distributed denial-of-service (DDoS) attack could flood the network with irrelevant traffic, interrupting a user's VR experience. Attacks could also manipulate content in ways that cause physical discomfort or disorientation.
Impersonation
VR headsets capture gesture and voice patterns. If attackers leverage behavioral data to impersonate a user, they could attempt unauthorized interactions with family members or perform other illicit actions under the user's identity.
Cyber Defense Practices
Although AR/VR adoption is not yet universal and many of the described incidents are not widespread, it is better to prepare now than to respond after an incident. Recommended cybersecurity practices for AR/VR organizations include:
- Configure AR/VR application tools for regular security assessment and auditing.
- Request explicit permission from users before collecting personal data.
- Deploy security monitoring at each device and interaction point.
- Use appropriate authentication methods when devices communicate with each other.
Some organizations have accelerated product development to gain market advantage without fully considering security implications. Simple devices can cause significant harm if compromised. AR/VR providers should analyze security risks, develop appropriate mitigations, and design robust systems to reduce the potential for abuse. Prioritizing security before new AR/VR use cases reach the market is essential.
 ALLPCB
ALLPCB