Access Control System Components
Identity recognition
The identity recognition unit is a key part of an access control system. It identifies and verifies persons requesting access. Common identification methods include card-based identification, password-based identification, biometric identification, and hybrid methods.
- Biometric identification: fingerprint, palm pattern, fundus, iris, finger vein, face, voice, signature, gait.
- Personnel code identification: standard keypad, scrambled keypad, barcode card, magnetic card, IC card, proximity card.
- Item feature recognition: metal objects, magnetic objects, explosives, radioactive materials, special chemicals.
- Item code identification: barcode, ESA tags, QR code.
Sensing and alarm
The sensing and alarm unit includes various sensors, detectors, and push buttons, and should incorporate measures against mechanical tampering. The most common devices in access control are door contacts and exit buttons; these devices typically output switch signals. A well-designed system can encrypt or convert door contact and exit button signals, for example to TTL levels or digital signals. The system should be able to monitor alarm states such as alarm, short circuit, secure, open circuit, request to exit, noise, interference, shielding, device open circuit, and tamper, to reduce the risk of deliberate signal masking or damage. Alarm circuits should be monitored in real time regardless of the system armed or disarmed state.
Processing and control
The processing and control equipment generally refers to the access control controller. The controller is the central unit, storing card numbers, passwords, and other access data. It performs processing and decision tasks for access requests and typically contains a processing unit, storage, input and output interfaces, and communication modules.
Locks and actuators
The locks and actuator unit includes electronic locks, barriers, and other control devices. These devices should operate responsively, execute reliably, resist moisture and corrosion, and have sufficient mechanical strength and anti-tamper properties. Electronic locks vary by working principle and include electric bolt locks, magnetic locks, cathode locks, anode locks, shear locks, and others, suitable for wooden, glass, and metal doors. Each lock type has different characteristics in security, convenience, and reliability, so selection should be based on the specific application.
Entry control actuators
Entry control actuators execute control commands from the access management subsystem to perform deny or allow actions at entries and exits. Common controlled devices include electric locks, barriers, alarm indicators, and motorized doors.
Wiring and communication
Access controllers should support multiple network communication methods such as RS232, RS485, or TCP/IP, allowing networked operation across local, national, or global scopes. For overall system security, communications must be encrypted, typically with at least 64-bit encryption.
Management and configuration
The management and configuration unit refers to the access control management software. Management software can run on Windows 2000, Windows 2003, and Windows XP, support server/client modes, and provide role-based authorization and management. It should use a robust database such as Microsoft SQL for scalability and integration. Typical functions include device management, personnel information management, badge printing, user authorization, operator permission management, alarm information management, event browsing, and electronic mapping.
Installation and Wiring Diagram Tutorial
Because access control systems are widely used, the following summarizes common installation steps and wiring practices to help understand system setup and commissioning.
Installation steps and wiring instructions:
1. Equipment installation
(1) Front-end devices
A. Install the reader at the entrance. Keep the reader away from high-frequency or strong magnetic fields (for example, heavy-duty motors or monitors), and coordinate grounding with the control box.
B. Install an exit button at the exit.
C. Install the electromagnetic lock at the top edge between the door and the frame.
D. For safety and aesthetics, the controller and power box may be installed on-site or in a low-voltage equipment shaft. On-site installation can reduce cable length; installation in a shaft facilitates maintenance and system security. The controller box may also be mounted above the reader near the lock. The specific approach should be chosen based on project requirements.
(2) Central control room equipment
A. Mount the control host and keyboard on a wall or place them on a workstation.
B. Position alarm devices where their alerting effect is optimal.
C. Because of the system's operational requirements, provide stable power such as a UPS for centralized power to the access control system.
2. Equipment commissioning
(1) After installation, connect one access reader to the host and test that reader alone for missed or false events. After verifying one channel, connect and test the next channel. Repeat until all channels are individually validated, then connect all lines.
(2) Administrators should assign permissions according to user roles, for example allowing some users unrestricted access while restricting others to specified times and areas. Verify that the central computer records normal and unauthorized openings.
(3) Test whether the controller can record events independently if the central computer is offline, and verify that all recorded data uploads automatically and intact when the central computer reconnects.
(4) Maintain detailed commissioning records.
(5) Complete the final acceptance report.
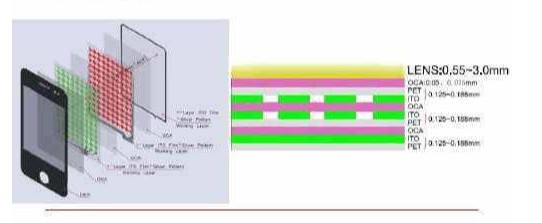
3. Cable installation
(1) Wiring should comply with applicable electrical installation and acceptance codes and other relevant standards. Cable pulling in conduits or trays should occur after finishing plaster and floor work. Remove water and debris from conduits before pulling wires. Do not route different systems, different voltage levels, or different current types in the same conduit or tray slot. Wires in conduits or trays should not have splices or knots; joints should be soldered in junction boxes or connected with terminals. Small-gauge connections may be twisted with at least five turns, tinned, and insulated with tape. Where wiring crosses building expansion joints, provide compensation; secure wires on both sides and leave appropriate slack. Terminal boxes should use crimped or soldered terminal strips with clear labels.
(2) Mount access controllers securely and level, with clear labeling. Reinforce installation on lightweight partitions. Cable entries to controllers should be neat, avoid crossing, and be firmly fixed. Label cable cores and connected conductors; terminal blocks should not have more than two wires per terminal; leave at least 20 cm of slack for cable cores and conductors; bundle and tie wires; seal the entry conduit after wiring.
(3) The controller main power should be connected directly to the supply; using removable power plugs is not recommended. The main power inlet should be clearly labeled. Controller grounding must be solid and clearly marked.
(4) The grounding bus routing and specifications in the monitoring room must follow design requirements. The bus surface should be intact without significant damage or solder residues; copper strip bus should be smooth and burr-free; insulation should show no aging or cracking. Lay the grounding bus centrally in the cable trench or tray and fix it in place; the bus should be flat without warping or bending. Connections between the bus and equipment racks should be secure. On cable trays, copper strip bus can be fixed with screws; braided copper bus should be tied to crossbars. Lightning protection and grounding installations must be executed strictly according to design and coordinated with civil works.
 ALLPCB
ALLPCB